What are SSH Keys?
SSH (Secure Shell) keys are a group of cryptographic keys used in the SSH (Secure Shell) protocol for secure authentication and encrypted connection between a pair of computing devices (such as the internet) over a network.
SSH keys comprise the public key, as well as the private key. The public key is distributed to all other parties while the private key is strictly kept securely with the user’s storage. An individual is requested to provide a public key of the remote system when they want to establish a safe connection with another element.
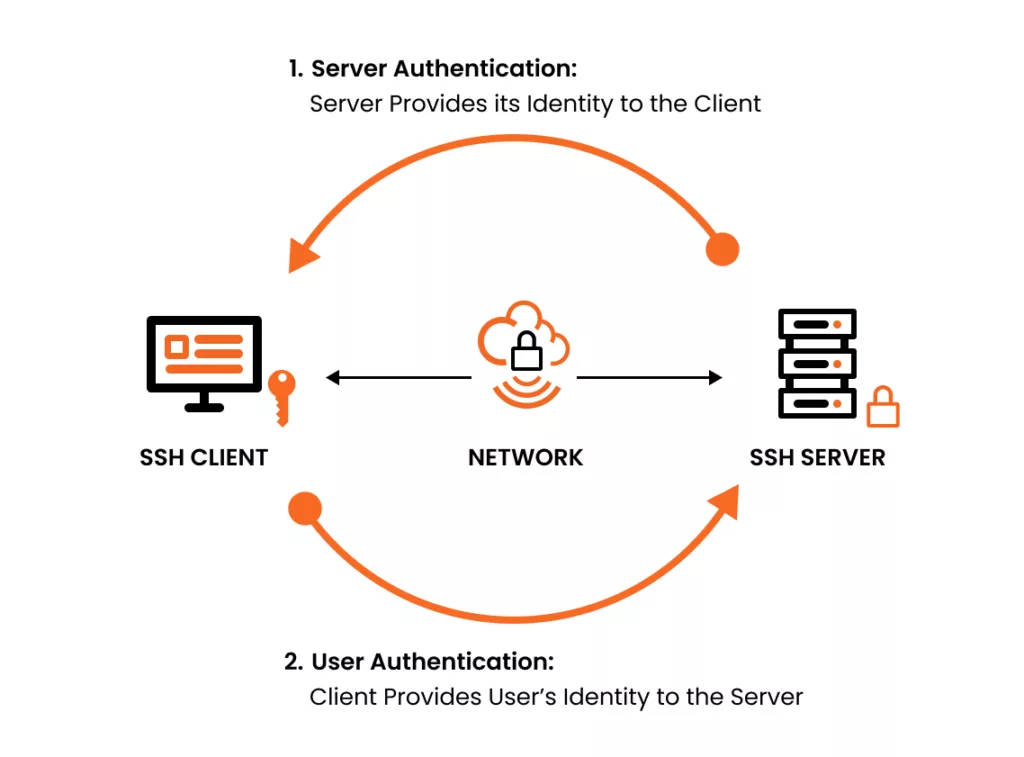
The remote system receives a public key corresponding to the user and after that encrypts a message with the help of this key and sends it back to the user. This key is employed to decrypt the message and thus syndicate the remote system’s identity to the user’s identification.
Types of SSH Keys
RSA (Rivest-Shamir-Adleman) Keys
The RSA (Rivest Shamir Aldeman) is a public-key cryptography that commonly produces those SSH keys (Secure Shell). Private and Public keys are being taken as pairs; keys are referred to as keys.
The public key is meant to be widely distributed to anyone who wants to be in contact with the owner of the private key, which has to be kept secret and only available for the person who owns it.
Recommended: What is an RSA Certificate? How RSA Certificate Works?
When a user wants to make an SSH connection to a particular server, he/ she provides their public RSA key to the server. In the next stage, the server accesses the user’s public key and uses it to encrypt an interesting message.
This can only be made possible with the user’s private key that is held only by them. This mechanism of this asymmetric encryption gives secure authentication of the client and setups a strong connection between client and server in the process. RSA keys are strong and are often used by SSH for strong communications.
DSA (Digital Signature Algorithm) Keys
DSA stands for the Digital signature Algorithm used for generating SSH keys (another asymmetric cryptographic service). DSA keys are similar to RSA keys with the only difference being that a pair of keys (public key and private key) are also generated.
Recommended: Public Key and Private Key Pairs: What are they and How do they Work?
The public key being the shared one, the private key then remains confidential. DSA keys are the most typical SSH keys used to authenticate or encrypt, especially on outdated SSH versions.
Meanwhile, they are the second choice for SSH implementations, surpassed only by RSA. DSA keys offer secured authentication and data encryption, but there are some drawbacks about these keys, like key length restrictions, and potential susceptibility of various attacks.
Consequently, RSA keys have become the common choice which many people use for SSH key generation.
What are the Risks of SSH?
SSH (Secure Shell) formerly has been known as a secure protocol for performing remote access, file transferring, and command execution, anything seen through one’s network.
Nevertheless, it acts as any other technology, although there are also some risks associated with it.
Some of the potential risks associated with SSH include:
Weak Authentication:
Another one of the major risks of SSH (Short Name for Secure Shell) security is related to poor authentication strategies like using basic or predictable passwords.
The case when hackers can simply guess or “bruteforce” the SSH credentials can lead to unauthorized access to the computer systems and consequently to the sensitive data exposure or malicious activity performance.
Man-in-the-Middle (MitM) Attacks:
MitM attacks involve the insertion of an attacker into an ongoing connection of two parties and maneuvering to intercept and tamper the communication between them.
In SSH, if the server’s public key is only verified by the client during the fist connection, it may leave a gap for hackers who act as the server to intercept or sniff the secrets which are exchanged between client and server.
Unauthorized Access:
If you do not apply proper SSH configurations, it can be used by an attacker to infiltrate your information systems and retrieve sensitive data.
For instance, open ports of SSH can be dangerous to the public internet if there are not proper access restrictions or firewall rules.
In such a case, access to servers can be gained by hackers and commands are executed for the purpose of violating the integrity of the system.
Weak Encryption:
Traditional SSH scripts (sometimes not updated/outdated) or applications with misconfigurations might use weak encryption algorithms or protocols which are subject to cryptographic attacks.
The lack of encryption or weak setup of it can put classified data, passwords or other keys to malefactors’ eye or decryption by attackers.
Vulnerabilities in SSH Software:
Just like any other software SSH may be vulnerable to bugs or flaws which will be caused by the attackers’ exploitation.
These flaws can give attackers an opportunity to gain access to device administrator accounts, execute arbitrary code, or cause harm on devices exposed to such software.
What is the Most Secure Way to SSH?
The most secure way to use SSH (Secure Shell) involves implementing a combination of best practices and security measures to protect against potential threats and vulnerabilities.
Here are some key aspects of a secure SSH configuration:
Disable Password Authentication:
Usernames and passwords should not be used for providing access anymore but rather SSH keypairs.
SSH keys are based on asymmetric cryptography that is considered to provide an easier security level than password-based access.
Through the creation of SSH keys, a pair of keys: public and private that is essential for the successful implementation of SSH is generated.
A public key is saved to the server, and a private key is used for the client machine protected with the highest level of security. This technique helps to prevent dictionaries attacks against the weak passwords.
Use Strong Passphrases for SSH Keys:
SSH keys should be generated by users with a really strong phrase as a passphrase in order to protect the private key.
Passphrase is another protective shield in this process by entangling the private key with password. This substantially increases the challenge especially for the attackers to take over the key.
It does not matter whether the attacker has gained access to the client machine, the key can still be kept safe.
Keep SSH Software Up-to-Date:
Software update on a routine basis, particularly SSH software and libraries, is as equally important as patching to address any known vulnerabilities and shield against potential cyber attacks.
The SSH protocol encrypts communication to prevent eavesdropping but it opens up an opportunity for the attackers who can use the SSH implementation vulnerabilities to gain unauthorized access or execute malicious commands on systems.
Therefore patching the security updates becomes important functionality to maintain a secure SSH environment.
Limit SSH Access:
Confine SSH accessing only to the trusted persons and networks. Put edges in place (e.g. firewall rules or networking access controls) that limit SSH connections to particular IP addresses or subnetworks.
Through this method, a smaller area where the vulnerabilities could be exposed is now possible. Therefore, unauthorized access is restricted, and threats are lowered.
Monitor SSH Access Logs:
Conduct an active control of access logs of SSH to find out the abnormal behavior. Observe the signals, for instance, the many login failures, the unusual connection patterns or password cracking attempts.
SSH mechanism must be implemented with logging and auditing advantages so that it will be able to promptly identify and promptly respond to any Security issues.
Implement Two-Factor Authentication:
Make 2FA for SSH keys mandatory as security risk is real and threats are coming from all sides.
Through 2FA, users are led to provide an extra proof of entry, counting on OTP tokens or biometric authentication, besides their SSH credentials.
Recommended: SSH Vs. SSL – The Technical Differences Explained
The additional security produced by this shield increases the reliability of the system as unauthorized access will not matter even if the SSH keys or passwords are misused.
Harden SSH Configuration:
Configure SSH server settings for security adhering to the best practice rules.
This will include all the aspects like disabling root access, limiting users privileges and applying the strong encryption algorithms and key exchange methods.
Consequently, think of applying defenses like these, for example, SSHGuard or Fail2Ban that are capable of automatically blocking IP addresses for hosts that behave suspiciously.
Regularly Rotate SSH Keys:
Regularly refresh SSH keys and frequently change passwords to reduce the possible chances that would happen due to key compromise or cases of insider threats.
Develop a key management policy that directs revocation of keys when employees terminate their contracts with the firm or there are risks of key compromise
SSH Security Best Practices
With the aim of providing protected SSH connections between the endpoints, securing encrypted sessions will be one of the most important factors to ensure the integrity and confidentiality of sensitive data transfer. Many SSH practices designed to elevate security would include them:
- First of all, try SSH keys which are based on key-based authentication not password especially.
- SSH keys provide a more secure method of authentication by using a pair of cryptographic keys: an element which is public and another element which is private.
- Apart from that, having strong passphrases is also recommended for guarding private keys during generation.
- Additionally, replacing and updating the SSH software and libraries used regularly is necessary for exposing and addressing common vulnerabilities and security issues.
- Make it a routine to gather and process alerts on security incidents as well as new trends on their prevention in the digital realm.
Frequently Asked Questions
What is an SSH key?
An SSH key is a pair of cryptographic keys (public and private) used to securely authenticate to remote servers without needing a password.
How do I generate an SSH key?
Run command ssh-keygen -t ed25519 -C “[email protected]”
This creates id_ed25519 (private) and id_ed25519.pub (public) in ~/.ssh/.
What is an SSH Agent?
An SSH agent securely stores your private key in memory and provides it automatically to SSH commands, so you don’t need to re-enter your passphrase.
What an SSH Key Means in GitHub?
SSH key in GitHub is a secure way to authenticate your computer with GitHub without using your username and password. It allows you to clone, pull, and push code over SSH using cryptographic keys instead of manual login.

