Encryption Vs Hashing Vs Salting – What’s the Difference?
The difference between Encryption, Hashing and Salting Explained
Almost everyone has followed the old-age practice of making things more secure, secret, and obscure. From time to time, the way we secure our items and information has been changing, but the fundamental practice behind it – not to let anyone else access it – remains steadfast.
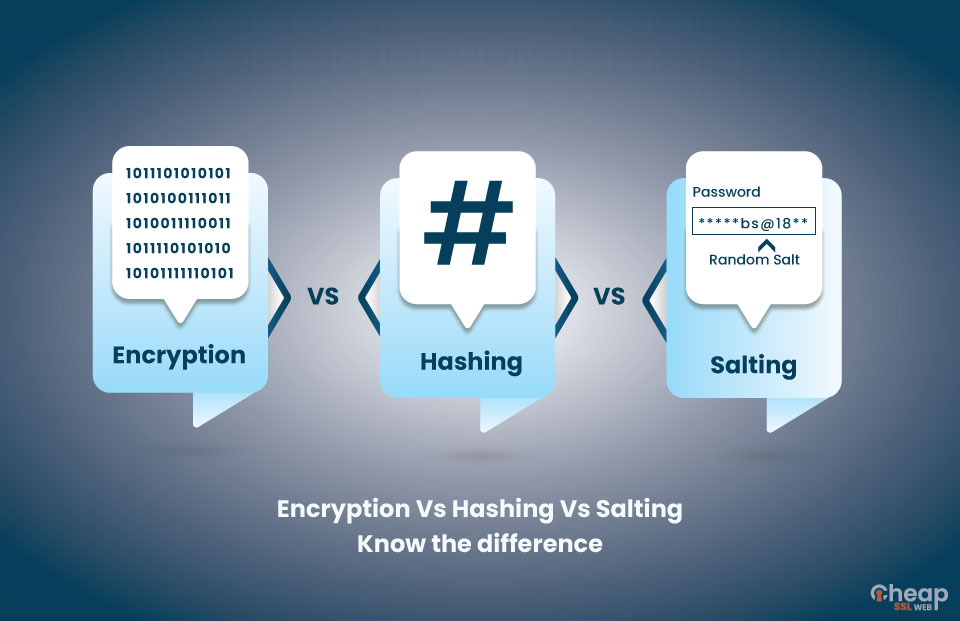
On the same line, encryption, hashing, and salting are three modern security techniques and systems we use today. In this guide, we will find the differences between encryption vs hashing vs salting.
In the cybersecurity world, people commonly use these three techniques. Encryption, hashing, and salting prevent information leaks and shield hackers from cracking passwords. These techniques share a common purpose. But there are several differences between them as well. Encryption is about encoding data accessible with a key; hashing is about irreversible calculations. In salting, we add random data to the main information and make it more secure for storage.
Let’s find out the difference between encryption and hashing and salting in some more detail.
What is Encryption?
Encryption scrambles the data lodged in plain text, converting it into another form of text called Ciphertext. Authorized people with access to the key can unscramble this ciphertext, returning it back into plain text.
So, this is like making simple text or plain text unreadable for the users. Unless you have the right or the key to decrypt it and read it. When you want to encrypt something and decrypt it later, always use encryption.
And this forms the basic distinction between encryption vs hashing (more on this later).
For encryption, we can use Cipher, which is an algorithm that encrypts and decrypts the information. A series of defined steps carry out the encryption and decryption process. The algorithm defines a set of rules, which are pretty simple.
It may surprise you to know that encryption is not a new technology. People have been using encryption since ancient times, and there are several examples of it being used throughout history. From the hieroglyphs to Caesar’s primitive shift cipher technique, encryption has been a part of several cultures.
Types of Encryption
1. Caesar Cipher
This is the simplest form of encryption where every letter shifts to a fixed position according to the set rules. If the rule is to shift the character’s position to the third place, every “a” will become “c,” and every “c” will become “e.”
The Caesar cipher is a type of Shift Cipher, which was used in the previous era. Besides this, other types of traditional cipher techniques that were used include;
- Substitution Cipher
- Transposition Cipher
- Polyalphabetic Cipher
- Nomenclature Cipher
2. Advanced Encryption Standard
The AES encryption system is a form of the symmetric-key algorithm. You might have read AES on popular instant messaging applications like WhatsApp. AES encrypts electronic data and secures it. It is a popular form of encryption system utilized not only in these applications but in various other situations, including communications.
3. Rivet-Shamir-Adleman
RSA is a form of encryption that people mostly use in publicly accessible platforms. Public-key cryptography used it as the first encryption system. This means that the RSA encryption allows people to communicate securely without having to know or meet each other previously.
4. Elliptic Curve Cryptography
The ECC type of encryption works on the principle of the algebraic structure of elliptic curves over a finite field. The major advantage of ECC is that it uses pairs of public and private keys to encrypt and decrypt data. ECC is popularly used as an alternative to RSA-type encryption.
5. Pretty Good Privacy:
Also called as PGP, this type of encryption and decryption technique combines different types of protection systems. You can also execute hashing by following the principles of PGP.
For further classification, we can also divide the modern encryption services into Symmetric and Asymmetric encryption. In symmetric encryption, every component secured has its own private key for accessing the contents. Symmetric encryption is something we have been using over time, and it has also created issues throughout time.
A public key system was necessary because handling and managing private keys posed issues and risks. A public-key system is the cornerstone of asymmetric encryption, where one public key encrypts and other private key decrypts.
With the encryption part done, let’s move to hashing. Go through the next section carefully to find out the difference between encryption and hashing.
What is Hashing?
In hashing, we essentially map data of different forms and types to create a key or hash value. Hashing is a one-way function, but encryption is a two-way function. You see, in encryption, we have the encryption and decryption function. But this difference also stems from the fact that hashing has a different function.
The hash function ensures that no one has altered the data, file, or information. In essence, the hash function serves as a verification mechanism. Therefore, when you digitally sign a document or intend to send a file over the internet, you can add the hash function to guarantee that the data or file has not been tampered with during the transfer.
Here’s how hashing ensures this no-tamper system. Assume that you have created a document and have digitally signed the same. Then you also want to make it available for others to download.
When following the hash function, you will create a hash of the piece of document and of your signature as well, separately. With this, the document and the signature assuring its authenticity are encrypted or protected.
At the time the user downloads the file, the browser they are using will decrypt it and run the same hash algorithm used to secure the file and signature. If the return values of the hash value after the mathematical calculation are the same, it implies that the document and the signature are not altered.
Still Confused?
Don’t worry! Understanding hashing is not easy; we know that. But you will get it completely after reading this.
First, don’t get confused with encryption and hashing; they are fundamentally different. In encryption vs hashing, you must understand the way these techniques work.
Hashing is about converting a plain text password into a string of characters or a hexadecimal number. This number or string of characters are unique to the given plain text. Plus, no matter the quantity of the text, whether it’s the entire text of an encyclopedia or a two-letter sentence, the supplied hash value will be unique to the text given.
So, suppose that you create a hash function for your password. The server will store the hashed version of the protected password at the time of creation. When you type in the plaintext of the password for accessing the account or file, the browser will run the hash function to identify the hash value from the same.
If the value matches the initial hash value generated while creating the password, access will be granted. Most importantly, since it’s a one-way function, reverse-hashing is not something you have to worry about. While it is technically possible, the chances of getting it done are negligible.
Read More on Why Password Salt and Hash Make for Better Security
Types of Hashing Algorithms
Just as there are encryption algorithms, there are different hashing algorithms. These are;
1. Message Digest 5
MD5 converts the plaintext into a 128-bit hash value. The message value can be of any amount of characters and quantities; the output value will be fixed. Before and after MD5, we have had MD4 and MD6, respectively. But all the MD level algorithms have been discontinued due to their vulnerabilities.
2. Security Hashing Algorithm
The entire web currently uses the SHA hashing algorithms the most. SSL/TLS certifications mostly use it, and it is almost impossible to tamper with the SHA algorithms. The US government developed two cryptographic versions of the SHA, SHA-1 and SHA-2, which result from the same algorithm.
SHA-1 was earlier used, but Google took two years and invested a lot of resources to find its vulnerabilities.
After this, we had SHA-2, which is currently used in most of the hashing-based encryption tasks. SHA-2 will generate an output value of 256 bits encryption with a 64-character hexadecimal string.
3. RIPMED
Several hashing algorithms are a part of this function having variable lengths. These include 128, 160, 256, & 320 bits.
4. WHIRLPOOL
This hashing algorithm created hash values of 512 bits. They have a 128-digit hexadecimal character, adding more security.
These aspects must clear the distinction between encryption vs hashing. Now when someone asks what’s the difference between encryption and hashing, you can confidently explain to them the answer.
Before moving to the next section, ensure that you understand the differences between hashing and encryption.
What is Salting?
Salting and hashing are related. The salting technique makes hashing more secure and robust. To enhance the security of your information online, you should salt plaintext by adding random data before running it through a hash function. This technique, called salting, can protect passwords against brute force attacks.
One of the most common uses of salting is securing passwords and giving them more resilience to any form of tampering, altering, and attacks. To protect passwords against brute force attacks, people specifically use salting as a technique.
And this is done for one purpose – to make cracking the password more difficult. Imagine you have created a hash value of the password. In salting, you will add random characters at the end of the hash value. Some of the most common salting algorithms include;
- Argon2
- Scrypt
- Bcrypt
- PKFD2
That’s it! Salting is simple and easy to understand.
To Sum it Up
The core of this guide was to understand the difference between encryption vs hashing. Encryption is a two-way function where you encrypt and need a key to decrypt the protected information. Hashing is a one-way function where you create a hash value of the plaintext and let the browser authenticate the contents. In salting, we add random characters at the end of the hash value to make it more obscure and tamper-proof.
While these three methods to protect information are different in the way they work and secure information, they are necessary today. With even the most robust organizations getting hacked, and these establishments devote massive resources to protecting their data, securing your information online is essential. With these techniques, we can easily make our information secure, protected, and difficult to hack or access without authorization.