Being a website administrator requires one to be aware of current trends and technologies in cyber security. However, if you are not familiar with certain concepts, the endless barrage of online information can get overwhelming. Choosing the encryption technique that best suits your website’s protection can be challenging in such a situation.
Ciphers, sometimes misspelled as ciphers, are an integral part of cryptography. The ancient Greeks are believed to have invented them around 400 BCE for encrypting military messages, and they have been in use ever since. Before we proceed with how this cipher or any modern ciphers work, let’s go over what ciphers are.
What is a Cryptographic Cipher?
Ciphers are cryptographic algorithms that can encrypt and decrypt information. Encryption refers to the act of converting readable information (“plaintext”) into unreadable or gibberish data (“ciphertext”).
Decryption simply reverses the processes by converting ciphertext back into plaintext. Most modern ciphers use an encryption key to encrypt and decrypt data.
Older ciphers like Caesar’s cipher operated with a much simpler logic. This specific cipher involves shifting each plaintext alphabet to the right by a certain number to convert it into ciphertext. Mathematically, we refer to this operation as the modulus and call the number by which the alphabets have shifted the key.
For example, if you were to run Caesar’s cipher on the following text with the key 4:
AppleIt would become:
ETTPITypes of Ciphers
We can divide ciphers into various categories based on their encryption mechanism and how they utilize it. The most common types of ciphers are:
Substitution Ciphers:
Substitution ciphers work by replacing characters in the plaintext with other characters for the generation of ciphertext. The above-mentioned Caesar’s cipher is an example of substitution cipher.
Transposition Ciphers
Transposition ciphers can be considered the opposite of substitution ciphers. Instead of replacing plaintext characters with alternates, they simply rearrange their positions.
Polygraphic Ciphers
Polygraphic ciphers are an advanced kind of substitution ciphers that substitute groups of letters instead of single characters. We do this to make it harder for attackers to guess the key by analyzing the frequency distribution of letters.
Permutation Ciphers
Permutation ciphers choose a random arrangement of the given plaintext characters. A permutation is a mathematical function that calculates all possible ways to arrange things.
Also Read: Block Cipher Vs Stream Cipher: Difference
Private-Key Ciphers
Private-Key ciphers were common among the earliest client-server network systems, and in this cipher, the sender and receiver both share a secret key beforehand. You can then use this key to encrypt and decrypt information. However, if the attackers got a hold of the private key, they could easily access privileged information.
Public-Key Ciphers
Public-Key ciphers are a modern iteration of private-key ciphers and are more secure. In this case, the sender and receiver have two separate keys – public and private keys. The sender encrypts the message using the public key and never really shares the private key across the web or with the receiver, which keeps it secure.
What is a Cipher Suite?
A cipher suite simply comprises a set of algorithms that secure connections across a network. These are used most commonly with the SSL or TLS protocols and are integral to the famous HTTPS connections.
What is SSL Cipher Suite?
An SSL Cipher Suite functions across the SSL protocol. The SSL or Secured Socket Layer protocol ensures authenticity between client and server systems in a process known as the SSL handshake. The handshake process decides the cipher suite to be used during the communication between the systems, and keys are exchanged.
The process effectively defends against man-in-the-middle attacks, which have been known for compromising connections for decades. The thing worth noting as a website administrator is that the server is the one that decides the cipher suite during the handshake.
Therefore, it is essential that you understand the appropriate cipher suite to accomplish the task for your website. It is also a good idea to consider the devices your target users use while choosing the suite.
If you’re wondering what an SSL Cipher looks like, here’s an example:
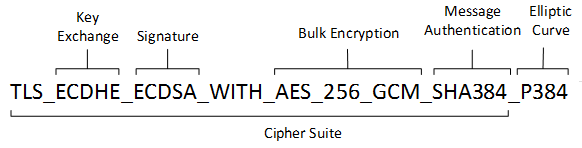
Components of SSL Cipher Suites
SSL Cipher Suites consist of four key components that establish a secure connection between the client and server systems. These are:
Key Exchange Algorithm
The key exchange is a symmetric encryption algorithm, which may seem counterproductive since SSL uses asymmetric encryption. However, the key exchange algorithm runs only after the initiation of the handshake and the authentication of both systems via asymmetric encryption.
Therefore, the key exchange algorithm functions as an additional layer of security and doesn’t have to be an asymmetric algorithm. Some common examples of key exchange algorithms are RSA, DH, and ECDH. In fact, most banking-related communications use the RSA algorithm for encryption, and it cannot be cracked without the aid of a Quantum Computer capable of running Shor’s Algorithm.
Bulk Encryption Algorithm
The Bulk Encryption Algorithm encrypts all the transferred data. To preserve time, the above-mentioned algorithms cannot be used. Instead, algorithms like 3DES or AES are employed due to their speed in encrypting and decrypting large volumes of information.
Authentication Algorithm
The client uses the Authentication Algorithm to authenticate the server’s identity. This is an extra precaution to prevent man-in-the-middle-attacks that take place on public networks. The most common algorithms used for this purpose are RSA and DSA.
Hashing Algorithm
Hashing Algorithms are used for an advanced form of cryptography known as hashing. In this process, the data is converted into an exact hash value of a certain length to ensure the integrity of the data is preserved over the network.
If the data has been tampered with, its hash value will be completely different from the original. Therefore, this would alert the systems of any malpractices taking place with the data.
Recommended: SSH Vs. SSL – The Technical Differences Explained
What is a TSL Cipher Suite, and How is it Different from an SSL Cipher Suite?
The TLS or Transport Layer Security protocol is an advanced version of the SSL protocol. Its functioning is similar when it comes to using Cipher Suites; however, it is more secure.
Here are the main differences between the two:
| SSL Cipher Suites | TSL Cipher Suites |
| Offers support for Fortezza Cipher Suites | Does not offer support for Fortezza Cipher Suites |
| Uses the “No Certificate” error message | It has several different error messages for various scenarios |
| The hashes include the master secret | The hashes are calculated during the handshake, making them more secure |
Seeing that the TLS Cipher Suite is a more recent iteration of the SSL Cipher Suite, it is a lot more likely that you will be working with the TLS variation. However, before you get to choose the right cipher suite for your website, let’s take a look at some of the most recommended ones:
Types of Cipher Suites
While talking about the various available cipher suites, we will skip over the ones that exist for TLS protocol iterations earlier than TLS 1.2. This is because newer versions have replaced and deprecated the previous iterations.
Here Are the TLS 1.2 Ciphers That Cybersecurity Professionals Recommend
- TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256
- TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
- TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256
- TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384
- TLS_DHE_RSA_WITH_AES_128_GCM_SHA256
- TLS_DHE_RSA_WITH_AES_256_GCM_SHA384
- TLS_DHE_RSA_WITH_AES_128_CBC_SHA
- TLS_DHE_RSA_WITH_AES_256_CBC_SHA
- TLS_DHE_RSA_WITH_AES_128_CBC_SHA256
- TLS_DHE_RSA_WITH_AES_256_CBC_SHA256
- TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305_SHA256
- TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305
- TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256
- TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305
While experts recommend and use the above cipher suites across the industry, they can still have certain vulnerabilities. As researchers discover exploits, they depreciate the respective suites.
As such, we recommend sticking to the cipher suites that come with TLS 1.3 since it is the latest iteration of the protocol, and its exploits would likely be harder to find.
TLS 1.3 Cipher Suites
- TLS_AES_256_GCM_SHA384
- TLS_CHACHA20_POLY1305_SHA256
- TLS_AES_128_GCM_SHA256
- TLS_AES_128_CCM_8_SHA256
- TLS_AES_128_CCM_SHA256
Read More on: TLS 1.2 and TLS 1.3 Supported Cipher Suites
Final Thoughts
SSL Cipher Suites, or most recently TLS Cipher Suites, are the first line of defense web servers have to protect their users’ data. These encrypt the information being communicated between the client and the server and preserve the integrity of the data.
In order to correctly preserve the security of data, choosing a cipher suite compatible with the most recent iteration of the TLS protocol is crucial.

