Hash Function in Cryptography – A Comprehensive Study

Hash Function in Cryptography — Get to know its Definition, Features, Applications, and Necessary Characteristics!
Security and privacy are the two chief components of the digital world. No matter what you search online, every website has some sort of background process that takes care of your data. One of those processes is the hash function in cryptography.
The hash function safeguards user data that websites acquire and serves as the guardian. Currently, if you log into a website with your username and password, the hash function securely ensures their protection. It shouldn’t be a surprise to you, keeping in mind the number of cyberattacks that happen these days.
One of the primary encryption techniques used against cyberattacks is the hash function. If you are not aware of it, this comprehensive guide is for you. Read along to find the definition, uses, and every last bit about the cryptographic hash function.
What is the Hash function in Cryptography?
So, for those of you who don’t know the hash function, let’s help you out! But before we get into it, here is what cryptography is.
Cryptography is a process that converts the plain message or data sent by a user into an unrecognized form. The trick here is that only the authorized user will be able to convert it back to the original form. A simple example of cryptography is the conversion of letters into special characters.
Input stream: I am John
Encrypted message: ! @# $%^&
Today, people use numerous types of cryptography techniques. Powerful encryption algorithms back these. Here are some of them!
- The hash function
- Public key encryption
- Secret key encryption
The hash function varies from the rest of the methods in various ways. Let’s see how!
The Hash Function
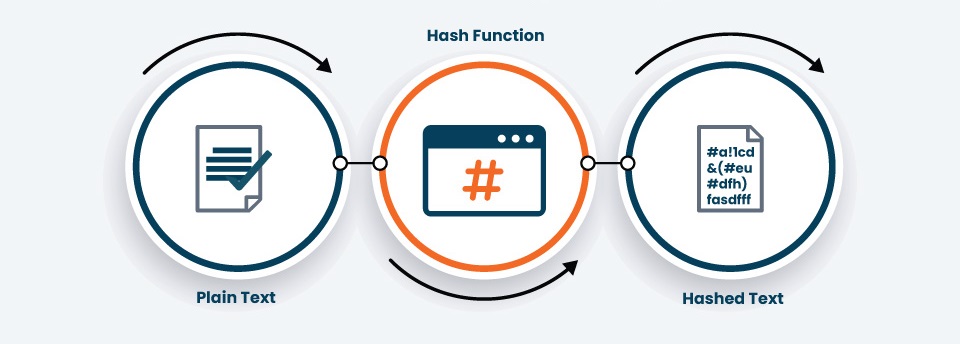
If we talk in layman’s terms, the hash function is an entity that converts a string of data into another encrypted string. The catch here is that the input string or data can be of any length. But, the output encrypted string is of a fixed length. The hash function produces a unique output string that cannot be reverse-engineered in any way.
The core goal behind using the hash function is to keep the data in an unrecognizable state. The authorized recipient can only interpret it. The hash function commonly produces values known as hash values, hash codes, hashes, and even digests.
Example of a hash function!
To understand the Hash function in cryptography, here is an excellent example!
The hash algorithm is used for encryption, and various hashing algorithms exist. The hash function’s output is a hash code of a fixed length. But, this hash code varies based on the type of algorithm used.
For example, there are various types of hash algorithms, namely.
- SHA-1 hashes
- The SHA-2 family of hashes
- The MD family
- NTLM
- Whirlpool
The SHA-1 hashes produce the output value of 160 bits. On the other hand, the SHA-2 family of hashes produces hash values of 224, 256, 384, or 512 bits.
The output of all the hash functions is in hexadecimal form and is independent of the size of the input. It means that if you input “Hello” into a Cryptographic hash, the output will be a hexadecimal hash, depending on the type of algorithm, of course.
Similarly, when you enter, “Hello, this is Skynet. We are here to conquer your planet.”, the output will be the hash value of the same length for the same algorithm.
A 160-bit hash value has around 40 hexadecimal characters. On the other hand, a 256-bit hash value has 64 hexadecimal characters.
How does the Secure Hash Algorithm in Cryptography work?
Don’t panic after reading the title of the section. The secure hash algorithm is SHA which has been described above. Let’s see how it works!
The method of hashing is pretty easy to understand. When you provide a string to a hash function, it is segregated into various equal segments. If the segregation is not possible with the string, padding of 1s and 0s is added.
It works like this!
Each block is hashed individually. But, all the blocks are correlated. The first data block is hashed and fed to the second block as input. The output hash of the second block is provided to the third block as input. This process carries on until the last block. The final output is the combination of all the data blocks.
You can clearly get an idea that if even one letter, character, or number is changed from the input, the entire output changes. So, if the messages have been tampered with, you will easily know.
If you input the string, “Hello, this is Skynet. We are here to conquer your planet.”, The output as per the SHA-256 bit Hash encryption will be:
B1c5bc76b5be514dc8b647aff3ffff94f9b4c6ed863b8717f99875e2140a3260If the same hash encryption is used to hash “Hello,” the hash code will be:
2cf24dba5fb0a30e26e83b2ac5b9e29e1b161e5c1fa7425e73043362938b9824This is all about the Secure Hash Algorithm in Cryptography!
The MD5 Algorithm
Apart from this algorithm, there are other algorithms too. If we take the MD5 algorithm, the hash digest will be shorter than the SHA algorithm. Here is the MD5 hash function output if “Hello, this is Skynet. We are here to conquer your planet.” is fed as input.
832dca080e4a26202a626749747dc15aThe Whirlpool Algorithm
If we consider the same string for the whirlpool algorithm, the following will be the hash digest!
Ed73d7f81d3ee8b102f3d15ec565a763a20ea02cc2a2574ea2076d74c86da4ae986c9c5f5d3d3005c776a185008ea4e8f201307e9202fb575ca9e7f8a09b66dcCharacteristics of a Strong Hash Function in Cryptography?
As of now, we have studied various hash functions but are all of them good for data security? Here are some characteristics that justify the strength of a good hash function!
Pre-image Resistance or Irreversible
If a hacker succeeds in reverse-engineering the hash function, there is no pro to it. Hence, an ideal hash function has to be irreversible. In technical terms, it needs to be preimage resistant. The term pre-image resistance means that it is infeasible to reverse the hash function to the original plain text version.
Avalanche Effect
The avalanche effect in terms of hash function means that the output is precisely dependent on the input. Even if the change in the input is of a comma or one character, the change in the output can be significant. Hence, if the message has been tampered with, it can be easily tracked.
Collision Resistance
Collision in terms of hash function signifies two identical outputs for two unique inputs. This is not a good thing about hash and can lead to the compromisation of data. Usually, it happens because the used algorithm is broken. Hence, it is insecure.
The risk in such a case is that someone can replace the original, genuine data with the malicious one. As the signatures are the same, no one would be able to spot the difference. Therefore, a hash function has to be resistant to collisions.
Deterministic
The best thing about the hash function is that it is deterministic. The term deterministic here signifies that the hash function output will be of fixed length. It doesn’t matter if the input is one word or an entire book.
Hash Speed
The speed of a hash function is also a critical factor. As hash functions are used for various purposes, different applications require different speeds. For example, a low-speed hashing function can be used if password hashing is the purpose. But, if the goal is website connections, a hash function with a faster speed is necessary.
What can a Hash Function in Cryptography do?
As we are well-versed in the definition, working, and characteristics of a hash function, here are some of its remarkable applications!
1. Data security
One of the key benefits of hash functions is data security. For example, if you are sending some messages or a mail to your friend and on the way it gets tampered with, your friend can know if it has been. They can use your provided digital signature to regenerate the hash and compare it with the original hash. In this process, data remains secure, and you will know when it is not.
2. Secure storage of passwords
When a website asks you to save the password, it does not store your password in plain text. The website uses a cryptographic hash to store the password. It is an excellent cryptographic hash function example.
Websites use hashing coupled with salting to store your password. Salting is a method that involves adding randomly generated characters to your data before hashing. It enhances the security of passwords.
3. Facilitates secure authentication
As the hash function allows secure storage of passwords, it can be used for authentication. Whenever a user enters their password, it can be converted into a hash digest and compared with the stored hash function.
What are the practical application areas of Hash Function?
There are numerous practical applications of the hash function, such as
- Online password and financial data storage
- Securing cryptocurrency and blockchain data blocks
- Data integrity in emails, software, and other applications
Conclusion
The hash function in cryptography is one of the intrinsic techniques used for data security. No matter how big your data is, the function will shrink it into a smaller version. The hash function has several benefits. However, it needs to have some key features for that, such as speed, collision resistance, determinism, and more!