Encoding Vs. Encryption: Explaining the Difference
In cybersecurity, encoding, and encryption are two essential techniques that play a key role in protecting data from third-party access. In addition, both these technologies incorporate an additional layer of security.
For example, data can be encoded before being encrypted, making it more difficult for an attacker to decrypt the data if they can access it.
Due to this reason, encryption Vs. encoding is often talked about in cybersecurity, and both terms are often used interchangeably.
What is Encoding?
Encoding is using a particular technique for changing data into a new format. It is a reversible process that usually involves applying popular techniques to encode and then decode it in its original format.
Encoding has been used where data cannot be transferred in its original form between applications and systems, thus keeping the data’s usability and integrity intact.
However, it is not used for securing data as it is quite easy to reverse it back to its original state, so it does not take much for any attacker to decode the data in case they already have some encoded data. So, encoding is not used for security purposes.
Examples of Encoding
These are some examples of encoding:
- Base64 Encoding: This is a commonly used technique for encoding binary data into ASCII text format and is often used for encoding data such as images, audio, and video files over a network or for storage in a database.
- URL Encoding: This is another type of encoding that encodes special characters in a website’s URL so that they are safely transmitted in the web space.
- Hexadecimal Encoding: This encoding technique represents binary data in a hexadecimal (base 16) format. Therefore, it is commonly used to represent binary data in a more human-readable form and is often used for debugging and troubleshooting.
- ROT13 Encoding: This simple form of encryption involves rotating the alphabet’s letters by 13 places. It is not considered secure but often used to obscure spoilers or other sensitive information.
- ASCII Armor: This technique encodes data in a format that is resistant to corruption or tampering and is commonly used for encoding digital signatures and other cryptographic data.
These are some examples of the encoding types used in cybersecurity. Encoding is an essential technique for protecting data, but it is not the same as encryption and does not provide the same level of security.
Now, let us take a closer look at encryption, something that one cannot think of the Internet without. This will help us understand encryption vs. encoding.
What is Encryption?
What makes the Internet a safe and secure place for the end-users is ‘encryption.’ It is a process of converting a piece of data or information that is unreadable and impossible for any cybercriminal or hacker to decode. But why is this process secure?
Encryption uses ‘cryptographic keys’ to encrypt the data at the client’s end. The receiver’s system may or may not use the same key to decrypt the data.
Types of Encryption
Depending on the type of keys used for the encryption and decryption of data, the process is divided into two categories:
Symmetric Key Encryption:
As the name suggests, this type of encryption is symmetric. So when the sender sends a piece of data to the receiver, they use a ‘private key’ to encrypt the data. Here, the information of the private key stays confidential between the sender and the receiver.
As the receiver receives the encrypted information, they use the same private key to decrypt it. Symmetric key encryption is often used in banking for encrypting personally identifiable information (PII) is required for transactions and data storage purposes.
Asymmetric Key Encryption:
Asymmetric Key Encryption is the opposite of the symmetric encryption method. So, in this process, the encryption key is public and available to all, but the decryption key is private and known only to the intended recipient.
This enables secure communication as there is no prior distribution of a shared secret key between the sender and the recipient.
The private and public keys are mathematically related, but it is computationally infeasible to determine one key based on the other. Asymmetric key encryption has been found to have a use case in digital signatures, Blockchain, and public key infrastructure (PKI).
Also Read: Symmetric Encryption vs Asymmetric Encryption Differences
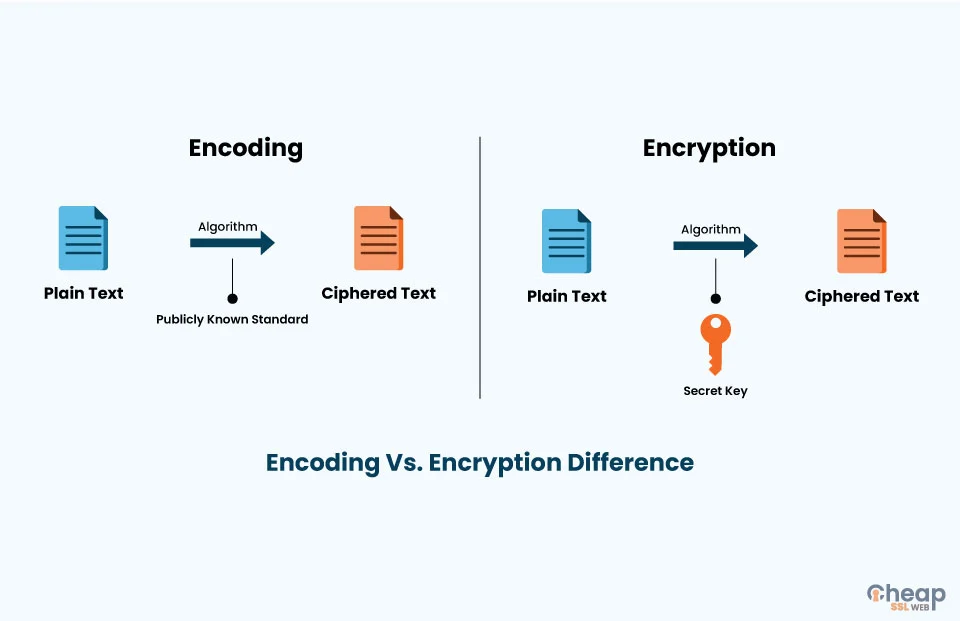
What is the Difference Between Encoding and Encryption?
The primary differences between encryption and encoding are as follows:
Purpose
Encryption is used to secure data, converting it into an unreadable format to protect it from unauthorized access. Encoding represents data in a different format to protect data integrity for storage or transmission.
Security
Encryption offers a higher level of security than encoding. The reason is quite simple. The former uses complex algorithms and a specific key to convert data into an unreadable format that is impossible for machines or humans to crack.
On the other hand, encoding converts data into a distinct format that is more human-readable, but when compared to its counterpart, it is quite possible for a machine or human to decode.
Confidentiality
Encryption protects and keeps sensitive information confidential, ensuring that only authorized parties can access the data. However, encoding does not offer the same level of confidentiality.
Algorithm
Encryption employs specific kinds of complex algorithms such as AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adleman), or DES (Data Encryption Standard) to encrypt the data.
Encoding, however, uses techniques typically simple and do not require a key to encode or decode data, such as Base64, Hexadecimal, etc., to represent the data uniquely.
Also Read: DES vs AES Difference
Reversibility
Encoding is reversible, meaning the original data can be recovered with the publicly available algorithm. Encryption, however, is a reversible process, so naturally, the original data can be recovered using the correct decryption key. Still, it is not publicly available like the former.
Key
Encryption uses public and private keys to encrypt and decrypt data. The private key is used to encrypt data, and the public key is used to decrypt it. No one can access the data without a public key as it is in an unreadable format.
Encoding does not use any key, so the encoded data can be retrieved or decoded by anyone with a proper grasp of tools or technologies, as they won’t need any key to decipher data.
Compliance
Different regulations like HIPAA (Health Insurance Portability and Accountability Act) and PCI-DSS (Payment Card Industry Data Security Standard) often require security regulations, thus ensuring the security of confidential information. However, encoding does not have to meet any security requirements.
Tamper Proofing
Encryption provides tamper-proofing of data, so if any unauthorized party tries to modify the data, it will be detected as the decryption of the tampered data will fail. However, encoding does not provide this level of tamper-proofing.
So, these are some of the differences between encoding and encryption. Here is a table for better understanding.
Encoding Vs Encryption Algorithm Comparison Table
| Parameters | Encoding | Encryption |
| What is it? | It is the process of transforming data into such a format that it can be by a different type of system using publicly available algorithms. | It is the process of encoding data securely so that only the authorized user who knows the key or password can retrieve the original data for everyone else; it is just a random string of characters. |
| Purpose | Protection of the integrity of data | Transforming data to keep it secret from others. |
| Used for | Maintaining data usability. | Maintaining data confidentiality. |
| Reverse Process | With the help of decoding, the original data can be retrieved. | With the help of decryption, the original data can be retrieved. |
| Key requirement | The encryption key is not required to decrypt the data and get the original data. | The encryption key is required to decrypt the data and get the original data. |
| Security Level | The security of the encoded is less as it can easily be decoded. | The encrypted data is more secure. |
| Compliance | It does not comply with any security regulatory bodies. | It complies with HIPAA and PCI-DSS for security regulations. |
| Tamper-Proofing | Encoding does not provide an encryption level of tamper-proofing. | Encryption provides tamper-proofing of data. |
| Example of Algorithm | ASCII, UNICODE, URL encoding, Base64. | AES, RSA, and Blowfish. |
| Application | Viewing special characters on the web page | Securely sending a password over the internet. |
Apart from these two terms, another term that confuses people is hashing, which is why there is a lot of confusion regarding encoding vs. encryption vs. hashing.
What is Hashing?
Hashing maps data of arbitrary size to data of a fixed size. It is a one-way function that takes an input and returns a fixed-size string of characters called the ‘hash value,’ ‘message digest,’ or ‘digital fingerprint.’
The same input will always produce the same hash value. However, even a small change to the input will produce a very different hash value.
So, which of these technologies is needed for your website? Let’s find out.
Also Read: Encryption Vs Hashing Vs Salting: Difference to Know
Concluding Lines
Understanding the differences between encoding, hashing, and encryption is essential. Using the wrong technique for a given situation can have serious consequences. Encryption and encoding are different processes serving different purposes in security.
For example, encoding to secure sensitive data would not provide any security, as the original data can be easily reconstructed from the encoded representation.
On the other hand, using encryption to compress and decompress data would be inefficient and unnecessary. Therefore, using the appropriate technique for a given situation is essential to ensure the data is protected and adequately transmitted or stored.
