ECC Vs RSA Certificate Difference Explained
ECC Vs RSA Certificate Difference: Decoding the Cryptographic Algorithm
When we talk about securing online communications, ECC and RSA are both encryption algorithms that are inevitable to mention. These algorithms are typically used in SSL/TLS certificates to ensure the security of communication that takes place in the digital space. So naturally, ECC vs. RSA might confuse many.
While buying an SSL certificate, the dilemma of ECC vs. RSA is something that confuses website owners. They would obviously want to make an informed decision to ensure maximum safety for their end users.
So how does one opt between the two types of encryption algorithms while buying an SSL certificate? Apart from that, what does each algorithm have to offer in terms of online security and data encryption? After all, that is what the bottom line is.
So let’s discuss ECC vs. RSA by starting with understanding the individual cryptographic algorithm.
What is RSA?
RSA stands for Rivest Shamir Adleman, and these are the names of the inventors of this cryptographic algorithm. Though it came into existence in 1977, in today’s time, RSA is widely used for encrypting emails, software, website data, etc. Its principle is based on the prime factorization method for one-way data encryption. The process involved taking two large random prime numbers and multiplying them together to develop a public key. It is known as the modulus, and though it is made public, one cannot determine what the message or piece of data was as the two prime numbers are kept private.
Here is a mathematical representation of how RSA works:
RSA encryption uses the principles of number theory and mathematical trapdoor functions to encrypt and decrypt data.
The encryption process begins with the selection of two large prime numbers, usually denoted as p and q. These two prime numbers are then multiplied together to create a modulus, n = pq.
A public exponent, which is usually denoted as e, is then chosen. This number should be relatively prime to the totient of n, which is calculated as: (p-1)(q-1).
The private key is then generated using the modulus, n, and another number, d, which is chosen such that (ed) mod (p-1)(q-1) = 1.
To encrypt a message, m, the sender raises it to the power of e mod n. To decrypt the message, the receiver raises the ciphertext to the power of d mod n. This process then results in the original message.
How difficult could it be to get hold of these two prime numbers, you might think? Actually, even if you think of trillions, it is too small of a number to represent them precisely. The difficulty is so much that it would take 1500+ years of computing time for sieving 768-bit, 232-digit RSA modulus using a ‘single core 2.2 GHz AMD Opteron processor with 2 GB RAM.’ Today, most SSL certificates employ a 2048-bit private key for RSA certificates.
What is responsible for making this encryption algorithm is its simple nature. Derived from a simple mathematical principle, it is highly suitable for ensuring data security on the Internet. As a result, it is widely used in a variety of applications, including secure communication, online banking and shopping, and electronic signature schemes. One of the advantages of RSA is that it can be relatively fast, particularly when used with shorter key lengths.
Features of RSA
- Asymmetric Encryption: RSA uses a pair of keys, one for encryption and one for decryption. As the encryption key is made public and the decryption key is kept private, it helps in establishing secure communication between two parties.
- Key Size: RSA keys can be generated with key sizes of 512, 1024, 2048, and 3072 bit. The larger its size, the more secure the encryption is.
- High Security: As it is based on the difficulty of getting two large and random prime numbers,RSA is considered to be one of the most secure encryption algorithms available. So without a private key, no one can decrypt the data.
- Digital Signatures: RSA is also used for creating digital signatures, which are used to prove the authenticity of a message or document.
Now let us understand ECC.
What is ECC?
ECC stands for Elliptical curve cryptography. As the name suggests, it is a form of an asymmetric cryptographic algorithm developed on the basis of the application of the elliptic curve’s algebraic structure over finite fields. The algorithm came into use when Neal Koblitz and Victor S in the 1980s suggested the application of elliptical curves in cryptography. However, ECC came into the limelight in 2004.
As it functions on the elliptic curve discrete logarithm problem (ECDLP), it is tough to crack since. Also, there has been no known solution to the mathematical problem given by the equation producing the elliptical curve in a graph. The only way intruders can launch an attack is a brute-force attack or a trial-and-error approach.
Structurally, ECC is more secure than RSA as it provides an optimum amount of security with a short key length, resulting in less computing power and network load. This translates into a better user experience.
In ECC, encryption and decryption are done using the points on the elliptic curve. The equation y²=x³ + ax + b is used to define an elliptic curve. It is a mathematical construct used in this cryptography. A set of points on the curve are chosen as a public key, and a private key is chosen as a point on the curve.
Different values of a and b can be used to create different curves, each with different properties, which can be used for different encryption purposes.
The point ‘a’ and ‘b’ are coefficients of the curve, and x and y are coordinates on the curve. The curve is defined over a finite field, and all points on the curve must satisfy this equation. The curve is also symmetric over the x-axis. It means that any point on the curve can be mirrored over the x-axis, and the curve will remain the same. Additionally, any non-vertical line will intersect the curve in three points or fewer.
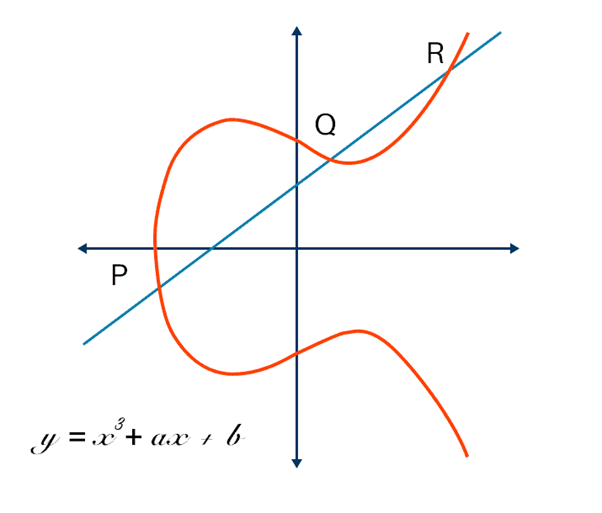
In the encryption process, a point on the curve called the public key and a second point called the private key are selected. Then a series of mathematical operations, such as point multiplication and point addition, on the public key and the plaintext message is done. This is done to produce a ciphertext.
The decryption process involves performing the same mathematical operations on the ciphertext and the private key. It helps in retrieving the original plaintext message. The security of ECC is based on the difficulty of solving the Elliptic Curve Discrete Logarithm Problem (ECDLP).
One of the advantages of ECC is that it can provide an equivalent level of security to other algorithms, such as RSA, with shorter key lengths. This makes it more resistant to certain types of attacks and more suitable for use in resource-constrained environments.
Overall, ECC is a widely-used and trusted encryption algorithm that is well-suited for use in a variety of applications, including secure communication, online banking and shopping, and in the IoT. It is known for its efficiency and scalability,
Features:
- Smaller Key Size: As ECC employs a small key size, it is quite efficient when it comes to memory usage and processing power.
- Same Level of Security: With a smaller key size of 256-bit, ECC provides the same level of security as RSA’s 2048 key length.
- Faster Performance: ECC is faster than RSA, so it is more suited for application in devices.
- Digital Signature: The places where digital signatures, such as digital documents and financial transactions, are used use ECC due to its faster computational speed. Moreover, they exhibit strong resistance to quantum computing attacks.
ECC is used in a variety of protocols, including SSL/TLS, SSH, S/MIME, and IPSec.
This was all about ECC. Now is the time to compare them based on different parameters and decide which is better or are both of them at par with each other. So let’s get started with elliptic curve cryptography vs. RSA.
RSA Vs. ECC: Difference Decoded
These are some of the differences of the elliptic curve vs. RSA.
● Key Length: ECC 256 vs RSA 2048
The key length of RSA is measured in bits, and it typically ranges from 1024 to 4096 bits. The longer the key length, the stronger the encryption. For RSA, a key length of 2048 bits is considered the standard that is secure enough for most applications.
When compared to RSA, ECC has a smaller key length compared to RSA. It is measured in terms of the size of the prime modulus, which typically ranges from 160 to 521 bits. For ECC, A key length of 256 bits is considered to be the standard.
| Security (in Bits) | Key Length of RSA | Key Length of ECC |
| 80 | 1024 | 160-223 |
| 112 | 2048 | 224-255 |
| 128 | 3072 | 256-383 |
| 192 | 7680 | 384-511 |
● Performance
The performance of ECC and RSA can differ in several ways:
–Encryption/Decryption: ECC encryption and decryption operations are faster than RSA due to the use of elliptic curve mathematics.
–Digital Signatures: Due to the application of elliptic curve mathematics, ECC digital signatures are faster than RSA
–Bandwidth: The demand for bandwidth is less with ECC compared to RSA when transmitting data over a network.
-Power Consumption: ECC drains less power than RSA, so it is more suitable for devices with limited power resources.
If we have to give you a number- RSA is capable of responding to 450 requests per second with a 150-millisecond average response time, but ECC takes only 75 milliseconds to respond to the same number of requests per second.
● Key Generation
ECC key generation is faster and more computationally efficient compared to RSA key generation. This is because ECC key generation involves choosing a random elliptic curve over a finite field and selecting a random point as the public key. On the other hand, RSA key generation involves the selection of two large prime numbers and performing mathematical operations on them to generate the public and private keys.
● Applications
ECC is used in various protocols, including SSL/TLS, SSH, S/MIME, and IPSec, whereas RSA is mainly used in SSL/TLS and SSH.
So these are some of the major differences between RSA and ECC. Here is a table for your better understanding.
| Rivest-Shamir-Adleman (RSA) | Elliptic Curve Cryptography (ECC) |
| RSA is one of the oldest and well-established public-key cryptography methods. | ECC is comparatively a newer public-key cryptography method. |
| Works on the principle of the prime factorization method. | Works on the mathematical representation of elliptic curves. |
| RSA runs faster as it is a simple algorithm. | As it is complex in nature, ECC takes more time to run. |
| Due to a lack of scalability, RSA has started becoming vulnerable. | ECC is more secure thanks to its adaptive phase. Its application might scale up in the future. |
| For implementing encryption, RSA demands bigger key lengths. | Compared to RSA, ECC demands shorter key lengths. |
| Standard Key length- 2,048 bits | Standard Key length- 256 bits |
| It supports all the platforms. | It exhibits compatibility with new browsers and OS (some platforms like cPanel are not supported) |
ECC vs RSA Certificates: Which Is Better?
Both ECC and RSA certificates are secure. But the choice between the two should be based on your organization’s specific needs and requirements.
When it comes to ECC Encryption VS RSA, the former is generally considered to be more secure than the latter due to several reasons mentioned above. On the other hand, RSA certificates have been widely used for decades and are considered to be more widely supported by older systems. So it ultimately comes down to your website requirements and system compatibility.

SECTIGO Essential SSL Wildcard at $49.99/yr.
Buy or renew Sectigo Essential SSL Wildcard at the lowest prices from the best SSL certificate provider at cheapSSLweb.com.
