Introduction
Today’s globalized and technologically driven world means that companies must pay close attention to protecting their data.
Two critical concepts have emerged as indispensable tools in this quest: Basic techniques such as asymmetric encryption and digital signatures have been the foundation of modern cryptography for some time.
Even though both elements are essential in protecting information, they work for different objectives and are based on contrasting principles.
This piece seeks to clarify these two emerging technologies and provide insights regarding which offers the best protection for your business against the increasing threat of cybercrime.
Asymmetric Encryption: Securing the Transmission of Sensitive Information
Asymmetric encryption, also known as public-key cryptography, encrypts data using a pair of mathematically related keys, a public key, and a private key, similar to the public and secret keys used in traditional RSA technology.
While the public key whose name it has is published to encrypt the information, the private key remains secret and is responsible for decrypting the encrypted information.
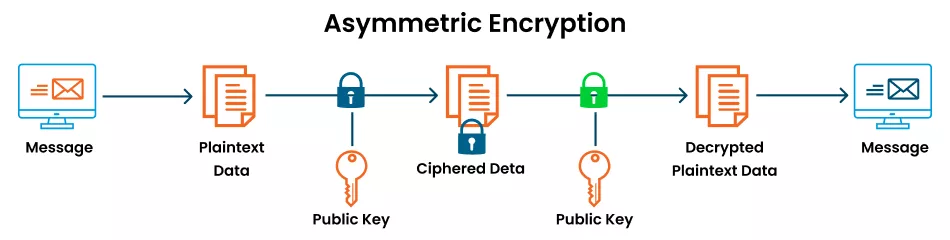
The process of asymmetric encryption unfolds as follows:
- Alice wants to send a confidential message to Bob.
- Alice obtains Bob’s public key and uses it to encrypt the message.
- Alice sends the encrypted message to Bob over an insecure channel like the internet.
- Bob receives the encrypted message and uses his private key, which only he possesses, to decrypt the message, revealing the original plaintext.
The idea here is that breaking asymmetric encryption is caused by the hardness of deriving the private key from the public key. Using modern computing capabilities, an attacker can try millions of keys per second but cannot open the message with the private key, which means the transmitted data is secure.
Cheap SSL/TLS Certificates~ Starts at $3.99/yr and Cheap Wildcard SSL ~ Starts at $39.99/yr
Decision-making is one of the security benefits offered by asymmetric encryption since it can be used to encrypt the two different keys and distribute the encrypted keys over the insecure channel.
Any two communicating parties who do not have a priori secret keys or secure channel to negotiate keys find this protocol especially useful. It also does away with the need for a secure exchange of keys, which can be proved to be complex and susceptible to forgery.
Furthermore, there is an aspect of scalability and flexibility inherent in asymmetric encryption that can be carried out and is much superior to the traditional symmetric encryption method.
On the other hand, in a symmetric encryption system, all the entities or members must use the same key, and this causes much complexity and insecurity as the number of participants increases.
Asymmetric encryption, also known as public key encryption, means that each party in a communication has a key pair of his own, and hence, it can work for all parties much better than the symmetric one.
Also Read: Symmetric Encryption vs Asymmetric Encryption
Digital Signatures: Ensuring Data Integrity and Non-repudiation
While one of the most common encryption techniques is applied to mask the content of data during transmission, the use of digital signatures provides a means of authenticating data and checking that it has not been tampered with.
Also Read: Digital Signature vs Digital Certificate
They made it possible to verify that the data has not been changed over time and that it comes from the stated source and, therefore, introduced a level of credibility and responsibility in digital communications.
Digital signatures also work on asymmetric encryption principles; however, their functions differ from encryption.
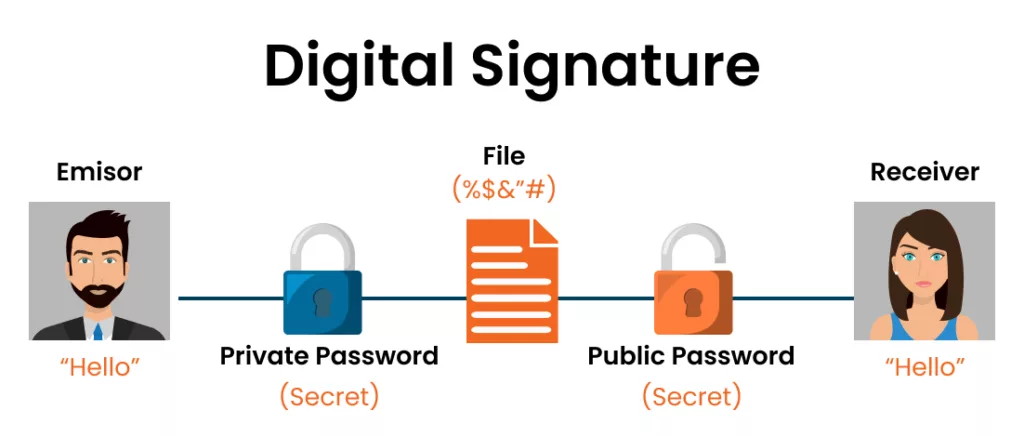
Here’s how they work:
- Emisor wants to send a signed message to Receiver.
- Emisor creates a digital signature by running the message through a mathematical function that involves her private key. This signature is unique to the message and Emisor’s private key.
- Emisor sends the message along with the digital signature to Bob.
- Receiver uses Emisor’s public key to verify the digital signature, confirming that the message originated from Emisor and has not been altered in transit.
If the signature is valid, Receiver is safe in the assumption that the message originated from Emisor and had not been modified. And, if the signature is wrong, then it may be concluded that the message was perhaps modified in transit or maybe it has not been sent by Emisor at all.
Digital signatures can also provide non-repudiation; once Alice signs a message, she cannot present her key to deny that she signed the message. This property makes it possible for digital signatures to be handy in legal, monetary, and financial negotiations and any other circumstances that call for credibility and responsibility.
Another main use of digital signatures is that they offer a solution to the problem of a ‘digital envelope’ and prevent the tampering of such files.
In contrast to tweaking a physical document that can be forged in any manner possible, digital signatures bring a unique certification code or digital fingerprint exclusively linked to the content of the data.
Any further change made to the data content would render the digital signature non-congruent, and this would help quickly identify any tampering that has been done.
In addition, digital signatures can be employed to encourage the manifestation of a link where a string of progressive signatures on the document or data is looked for.
This is particularly helpful in cases like negotiating orders and sales, distribution, use of copied software, and situations in compliance with regulatory frameworks.
Exploring the Differences and Use Cases
Symmetric encryption and hash functions are quite like asymmetric encryption and digital signatures however, they are designed for different purposes and are used in different ways.
Here’s a closer look at the key differences between the two:
Purpose:
- Asymmetric Encryption: Encrypts data to ensure the data is kept secure while being transmitted across the secure socket layer by sending the data through the public key of the recipient.
- Digital Signature: Verifies the authenticity and integrity of digital data by creating a unique signature using the sender’s private key.
Key Usage:
- Asymmetric Encryption: A sender’s private key is utilized to encrypt the message, while the recipient’s public key is used to decrypt the message.
- Digital Signature: It simply means that while generating the signature, the sender’s private key is used, and the signature can further be verified using the sender’s public key.
Data Protection:
- Asymmetric Encryption: This is advantageous for securing data during transmission as only the recipient with the key to decode the code can access the message.
- Digital Signature: This helps to keep the data accurate and provides the recipient with the ability to prove that the message they received is genuine, the sender cannot also deny having sent the message.
Use Cases:
- Asymmetric Encryption: Often used in top secret messaging like email, online chatting, etc., and secure file transfers where secrecy is paramount.
- Digital Signature: Long associated with legal and financial fields, distribution of software and documents where the use of digital signature is convenient and proves the identity of the person or organization using it and cannot be denied in the future or other words, doesn’t allow repudiation.
As for the difference in asymmetric encryption and digital signatures, while the two differ in functionality, they are commonly used in parallel to ensure a steadfast security solution.
For instance, in secure email communication, while sending the message, it can be encrypted with the public key, and to decode it, the private key can be used, thus ensuring that only the recipient can read the content while data integrity can be achieved by using a digital signature for the message.
Importance of Key Management
Symmetric encryption and block ciphering are based on secret keys, while asymmetric encryption and digital signature use public and private keys.
The key among these systems is the private key because its loss can be a major disaster, resulting in unauthorized deciphering of information or even emulating digital signatures.
Effective Key Management involves Several Key Principles:
- Key Generation: Random, secure, and unpredictable mechanisms must generate cryptographic keys to reduce the likelihood of an attacker generating the same keys as the user.
- Key Storage: Private keys are sensitive due to their capability of allowing unauthorized users to access secure systems and thus, they are usually stored in HSM and encrypted storage.
- Key Distribution: The public keys need secure ways to disseminate them and ensure that the keys are not substituted or one is substituted with another in a man-in-the-middle attack.
- Key Rotation: Cryptographic keys are sometimes utilized in a scenario and should thus be periodically changed or replaced if one is compromised.
- Key Revocation: Contingency plans should be present and follow certain rules that will dictate how the keys will be recalled and replaced in the shortest time possible to reduce the effects of key compromise.
Combining Asymmetric Encryption and Digital Signatures for Enhanced Security
It is widespread to use both asymmetric encryption and digital signatures when addressing real-world scenarios to add layers of protection.
This makes it possible to ensure that the privacy and accuracy of the data transmitted through the channel are well protected because the technique employs a combination of secure methods.
Here’s how the two technologies can be used together:
- Alice wants to send a confidential and signed message to Bob.
- Alice creates the message and generates a digital signature using her private key.
- Alice encrypts the message and the digital signature using Bob’s public key.
- Alice sends the encrypted package to Bob.
- Bob decrypts the package using his private key, revealing the message and the digital signature.
- Bob verifies the digital signature using Alice’s public key, confirming the authenticity and integrity of the message.
With the use of asymmetric encryption, the message is only accessible by the intended recipient, and this is protected during the time of transferring it where it cannot be intercepted by others (as explained above), while the digital signature can be used to ensure that the message has not been tampered with or it originated from the sender. This method covers all aspects of security needs; the confidentiality and integrity of data are safeguarded.
Conclusion:
Learn about data protection and get familiar with the basic measures that you should take to ensure your digital resources are safe. Discover our wide-ranging catalog of encryption and digital signature solutions to prevent possible risks to your content.
By comparing these two technologies, you can decide how to safeguard your critical data, mainly depending on the most efficient features.
Frequently Asked Questions:
Can Asymmetric Encryption be used for Digital Signatures?
Yes, asymmetric encryption and digital signatures are two that follow the same fundamental concept of public-key cryptography.
However, while asymmetric encryption is used to secure the transmission of the data, the digital signatures are used to address the issue of authenticity and data integrity. The purpose and usage vary in the two technologies.
Is Asymmetric Encryption more Secure than Symmetric Encryption?
These are the advantages of using symmetric and other disadvantages associated with both asymmetric and symmetric encryption systems.
The key distribution is safer in asymmetric encryption than in symmetric encryption, but upon transmission of extensive data, the aggregated encryption slows down the process.
In real-world applications, it is expected to deploy a combination of both asymmetric and symmetric encryption where key exchange is performed by asymmetric encryption while data encryption is performed symmetrically.
Can Digital Signatures be forged?
The latter is true because producing a genuine digital signature without possessing the private key is virtually impossible. However, if the private key is lost, an attacker could easily fake signatures, regarded as inconsequential, as in the essay.
This is why administrators need to be extremely careful when protecting private keys and follow specific guidelines that will help them ensure the security of the key — for example, by using specialized appliances known as hardware security modules (HSMs) and implementing strict access restrictions.
Are Digital Signatures Legally Binding?
Digital signatures imposed in the legislation of many countries are equal to traditional ones under some conditions, including, for example, the presence of a qualified certificate from a Certificate Authority (CA) or the admissibility of being achieved with the help of an accepted cryptographic algorithm.
That is why digital signatures are commonly used in legal services, financial services, and governmental bodies for electronic contracting and document signing.
Can Asymmetric Encryption and Digital Signatures be used together?
Yes, asymmetric encryption and digital signatures form good partners in that asymmetric encryption is combined with digital signatures to offer clients comprehensive security solutions.
For example, while the data transmitted over the network needs to be encrypted to ensure confidentiality, asymmetric encryption can be used. On the other hand, the content of the message needs to be verified with a level of certainty, and digital signatures can be used to ensure the integrity of the data as well as the confidentiality of the same.

