Credible authentication mechanisms must be addressed with digital space characterized by data security and integrity at stake. One such type is a mechanism such as a digital signature algorithm (DSA), a cryptographic method with authenticity, integrity, and non-repudiation of electronic data.
What is Digital Signature Algorithm (DSA) in Cryptography?
The Digital Signature Algorithm (DSA) is one of the most prominent methods based on creating and verifying digital signatures. A digital signature represents an array of mathematical schemes for authenticating and ensuring the integrity of digital data. Thus, emails and documents can be signed.
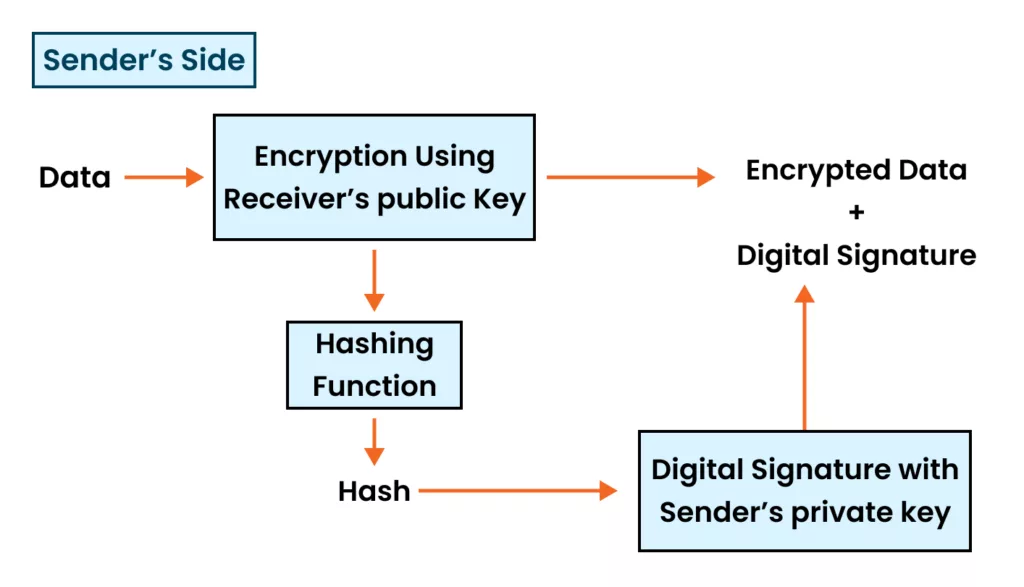
The DSA is based on the principles of public-key cryptography, which involves using public and private keys. The credentials of the private key construct the digital signatures, while the connected public key confirms their validity.
The DSA algorithm operates because the complex computational process of computing a discrete logarithm for a large prime number is complex. This issue has a private key as the exponent and the base result (public key) as given. The complex task of the DSA is precisely what serves as a basis for the system’s security.
Digital Signature Algorithm Example
The example that will be discussed is straightforward for understanding the DSA. Imagine Bob gives a cryptographic message that its authenticity cannot be denied while rolling an email.
Here’s how the process would work:
- Alice compiles a message and uses a cryptographic hash function SHAE-256 to compute its hash value.
- Alice “secondary” the hash value with her private key through the DSA algorithm, and she makes a digital signature.
- Alice, the sender, then generates and distributes the original text, the digital signature, and the document security code to Bob, the recipient.
- Bob gets the text and the digital signature authorized.
- Bob uses the same hash function (SHA-256) to calculate the hash value of the received message—link to the function ->.
- Bob implements the digital signature code using the DSA algorithm and Alice’s public key.
- If the authentication is okay, Bob can then have absolute confidence that the message originated from Alice and was not altered during transmission.
How DSA Works?:
The DSA has a few chunks for creating and checking digital signatures. Here’s a detailed overview of the process:
Key Generation:
- Select appropriate prime numbers ‘p’ and ‘q’ such that ‘q’ is a prime divisor of (p-1).
- Select a generator ‘g’ of order ‘q’ in the finite field modulo ‘p’.
- Select a random integer ‘x’ between 1 and (q-1). This is the private key.
- Calculate the public key ‘y’ as y = g^x mod p.
Signing:
- Hash the message using a cryptographic hash function like SHA-256 to obtain the message digest ‘m’.
- Select a random integer ‘k’ between 1 and (q-1).
- Calculate ‘r’ as r = (g^k mod p) mod q.
- Calculate ‘s’ as s = (k^-1 * (m + x*r)) mod q.
- The digital signature is the pair (r, s).
Verification:
- Receive the message, the digital signature (r, s), and the signer’s public key ‘y’.
- Hash the received message using the same hash function to obtain the message digest ‘m’.
- Calculate ‘w’ as w = s^-1 mod q.
- Calculate ‘u1’ as u1 = (m * w) mod q.
- Calculate ‘u2’ as u2 = (r * w) mod q.
- Calculate ‘v’ as v = ((g^u1 * y^u2) mod p) mod q.
- If v = r, the signature is valid; otherwise, it is invalid.
The uniqueness of the DSA algorithm is that it is based on the computational difficulty of solving the discrete logarithm problem, a feat that is logically impossible and, therefore, very secure. This means that an attacker will never be able to work out the private key given the public key or forge a valid digital signature.
Which is Better: RSA or DSA Digital Signature?
Additionally, both RSA and DSA are widely used digital signature algorithms; their performance characteristics may vary depending on the mathematical principles underlying them.
RSA is constructed on the fact that prime numbers with huge sizes are hard to factor in, whereas DSA is built on the problem of solving the discrete logarithm problem.
In this paradigm, the discrete logarithm problem is viewed as being harder to solve than integer factorization of large prime numbers, which leads to the conclusion that DSA is more secure for a certain key length.
Also Read: What is the COMODO RSA Certification Authority?
On the other hand, RSA can be applied either to encryption or to signatures. At the same time, DSA is utilized primarily for a signature-signature. Furthermore, RSA is faster overall for signature verification than DSA, where DSA is fast for signature generation.
The decision between RSA and DSA depends on which features based upon the application are most important: security level, compatibility with existing systems, and performance.
Also Read: ECC Vs RSA Certificate Difference Explained
RSA encryption can be a Greater choice than DES in those cases where encryption and digital signatures are required. In this case, the focus will not compromise the confidentiality of the digital signatures, and DSA will be a better option if performance is the primary concern.
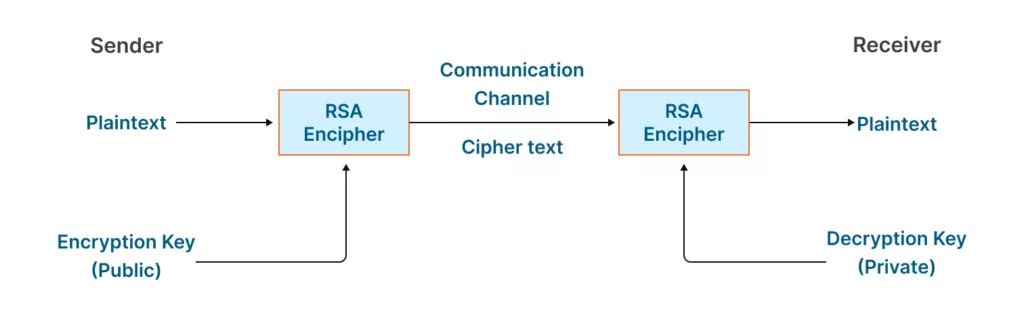
It must be stressed that both algorithms are widely known and achieve proper strength based on critical lengths and parameters whenever appropriately used.
Different scenarios may require other security protocols that should be carefully investigated during risk assessment, such as applying RSA or DSA at the end of the process.
What is the NIST Digital Signature Algorithm (DSA)?
The National Institute of Standards and Technology (NIST) Digital Signature Algorithm (DSA) is a version of the DSA algorithm, for instance. It is a government-developed cryptographic algorithm operating under NIST and Federal Information Processing Standard (FIPS) 186-4.
The NIST DSA introduces minor modifications to the DSA algorithm, such as utilizing other parameters and hashing functions. It also lists different security requirements and guidelines, such as procedures for key generation, signature creation, and signature verification.
The NIST DSA deviates from the original DSA in two fundamental ways: the algorithm uses hash functions. The NIST DSA standard recommends using either SHA-256 or SHA-3 hash functions, which the experts believe are more secure and robust than the earlier used SHA-1.
The other conspicuous distinction is a key length restriction. The NIST DSA lays out the minimal key sizes, considering different levels of security, to stay consistent with escalation in computational power and cryptanalytic algorithmic capability.
NIST DSA is famous and widely used in many applications and systems, including the governmental and military sectors. These sectors are like DSA due to their evident and presumable formal and stable requirements.
Indeed, it has a well-documented and standardized implementation of the DSA algorithm, which implies that it can guarantee interoperability and compliance with security best practices in the field.
Pros and Advantages of Using the Digital Signature Algorithm
The Digital Signature Algorithm offers several advantages and benefits, making it a popular choice for ensuring data authenticity and integrity:
Authentication:
Digital signatures are an efficient technique for confirming that a message or document sent by the sender is legitimate by obtaining his or her information, acting as authenticating data.
Integrity:
DSA guarantees secure transmission of the data; it is not possible for it to be altered or hacked. The digital signature technology in an interplanetary environment guarantees that any attempt to modify the data will be exposed easily since it will be invalidated and detected.
Non-repudiation:
After the digital message or document is signed, the originator cannot disclaim having produced it, giving non-repudiation for the information transmission source. These things are real in a legal setting and in contracts.
Encryption-independent:
DSA is a signature algorithm that does not need operational encryption. It can work with or without further security measures such as the AES or RSA system that allows strong secrecy of messages.
Standardization:
DSA is one of the standard encryption algorithms that guarantee universality, as it is universally agreed upon, and universal interoperability between different systems and platforms.
Scalability:
DSA can be implemented via different keys, enabling users to increase security and meet their needs. It takes more time to decrypt data, which may result in performance issues. Lengthener keys may be a choice and means to support better security.
Forward Secrecy:
DSA requires forward secrecy as its private key comprises previous messages and contents that remain unchangeable and untouched regardless of their secret key irregularities.
Efficiency:
DSA is traditionally as effective as RSA for signature generation, reducing the time spent on this purpose in applications that frequently need signing operations, like real-time systems or systems with many transactions.
Hardware Acceleration:
DSA can be available for notably rapid processing through special-purpose hardware implementation, which further boosts its performance and suitability for the most rigid performance-critical products.
Conclusion
Digital Signature Algorithm (DSA) is a significant cryptographic element in the field of digital security. It helps to ensure that digital data is authentic and not altered and that denying that a specific person signed it is impossible.
Whether you are trying to secure your documents, fasten your transactions, or encrypt your data, the DSA provides a reliable option that can cover all your digital assets.
DSA is natively supported by various cryptographic libraries and software applications, earning the trust of a wide range of industries. The combination of mathematical innovations, such as cryptography and the proof of the discrete logarithm, makes it possible to resist any data leak or hacking.
Significantly, the significance of the Digital Signature Algorithm in the rapidly changing digital landscape will only increase in tandem with its growth. Keep abreast of today’s DSA to secure your digital possessions while protecting the legitimacy of tomorrow’s internet world.
Frequently Asked Questions:
Can DSA be used for Encryption?
The DSA of the ECDSA is not his role, and the ECDSA as a whole considers the process of signatures and verification of the digital certificate, unlike the latter, which is notably designed to encrypt information. Encryption is the focus area in which DSA can be added to enhance the security features of other algorithms like AES or RSA’s algorithms.
Is DSA still considered Secure?
Of course, the DSA algorithm is still considered a secured digital signature algorithm whose security usually depends on correct key lengths and factorization parameters. Let’s talk about the same sort of cryptographic algorithm. The security level can decrease as computer power and cryptanalysis tools improve.
Can DSA be used with any Hash Function?
When DSA is meant for generalized use, appropriate hash functions can be selected without restrictions among all the cryptographic hash functions. However, an implementation standard usually specifies recommended hashing functions for advanced DSA.
For instance, the NIST ECDSA standard suggests using SHA-256 or SHA-3 hash functions. The sentence has been rephrased to enhance its structural integrity and improve reading comprehension.
Is DSA faster than RSA for Digital Signatures?
DSA is quicker than RSA when a message needs to be signed. Yet RSA is more suitable for signature verification. Nevertheless, this gap will widely depend on the unique designs built upon the algorithms, key sizes, and hardware contexts.
Can DSA Signatures be Revoked or Invalidated?
The DSA signatures can be annulled or voided if the private key is disclosed, and the signer’s personality is invalidated. In such cases, the information on the unacceptable behavior and the certificate revocation can be “pushed” out via the certificate revocation lists (CRLs) or other means.